Hackers abuse .arpa DNS and ipv6 to evade phishing defenses

Threat actors are abusing the special-use “.arpa” domain and IPv6 reverse DNS in phishing campaigns that more easily evade domain reputation checks and email security gateways.
The .arpa domain is a special top-level domain reserved for internet infrastructure rather than normal websites. It is used for reverse DNS lookups, which allow systems to map an IP address back to a hostname.
IPv4 reverse lookups use the in-addr.arpa domain, while IPv6 uses ip6.arpa. In these lookups, DNS queries a hostname derived from the IP address, written in reverse order and appended to one of these domains.
For example, www.google.com has the IP addresses 192.178.50.36 (IPv4) and 2607:f8b0:4008:802::2004 (IPv6). Querying Google’s IP of 192.178.50.36 via the dig tool resolves to an in-addr.arpa hostname and ultimately a regular hostname:
; <<>> DiG 9.18.39-0ubuntu0.24.04.2-Ubuntu <<>> -x 192.178.50.36
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 59754
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;36.50.178.192.in-addr.arpa. IN PTR
;; ANSWER SECTION:
36.50.178.192.in-addr.arpa. 1386 IN PTR lcmiaa-aa-in-f4.1e100.net.
;; Query time: 7 msec
;; SERVER: 127.0.0.1#53(127.0.0.1) (UDP)
;; WHEN: Fri Mar 06 13:57:31 EST 2026
;; MSG SIZE rcvd: 94
Querying Google’s IPv6 address of 2607:f8b0:4008:802::2004 shows that it first resolves to an IPv6.arpa hostname and then a hostname, as shown below.
; <<>> DiG 9.18.39-0ubuntu0.24.04.2-Ubuntu <<>> -x 2607:f8b0:4008:802::2004
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 31116
;; flags: qr rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa. IN PTR
;; ANSWER SECTION:
4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa. 78544 IN PTR tzmiaa-af-in-x04.1e100.net.
4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa. 78544 IN PTR mia07s48-in-x04.1e100.net.
;; Query time: 10 msec
;; SERVER: 127.0.0.1#53(127.0.0.1) (UDP)
;; WHEN: Fri Mar 06 13:58:43 EST 2026
;; MSG SIZE rcvd: 171
Phishing campaign abuses in .arpa domains
A phishing campaign observed by Infoblox uses the ip6.arpa reverse DNS TLD, which normally maps IPv6 addresses back to hostnames using PTR records.
However, attackers found that if they reserve their own IPv6 address space, they can abuse the reverse DNS zone for the IP range by configuring additional DNS records for phishing sites.
In normal DNS functionality, reverse DNS domains are used for PTR records, which allow systems to determine the hostname associated with a queried IP address.
However, attackers discovered that once they gained control over the DNS zone for an IPv6 range, some DNS management platforms allowed them to configure other record types that can be abused for phishing attacks.
“We have seen threat actors abuse Hurricane Electric and Cloudflare to create these records—both of which have good reputations that actors leverage—and we confirmed that some other DNS providers also allow these configurations,” explains Infoblox.
“Our tests were not exhaustive, but we notified the providers where we discovered a gap. Figure 2 depicts the process the threat actor used to create the domain used in the phishing emails.”
To set up the infrastructure, the attackers first obtained a block of IPv6 addresses via IPv6 tunneling services.
Source: Infoblox
After gaining control of the address space, the attackers then generate reverse DNS hostnames from the IPv6 address range using randomly generated subdomains that are difficult to detect or block.
Instead of configuring PTR records as expected, the attackers create A records that point those reverse DNS domains to infrastructure hosting phishing sites.
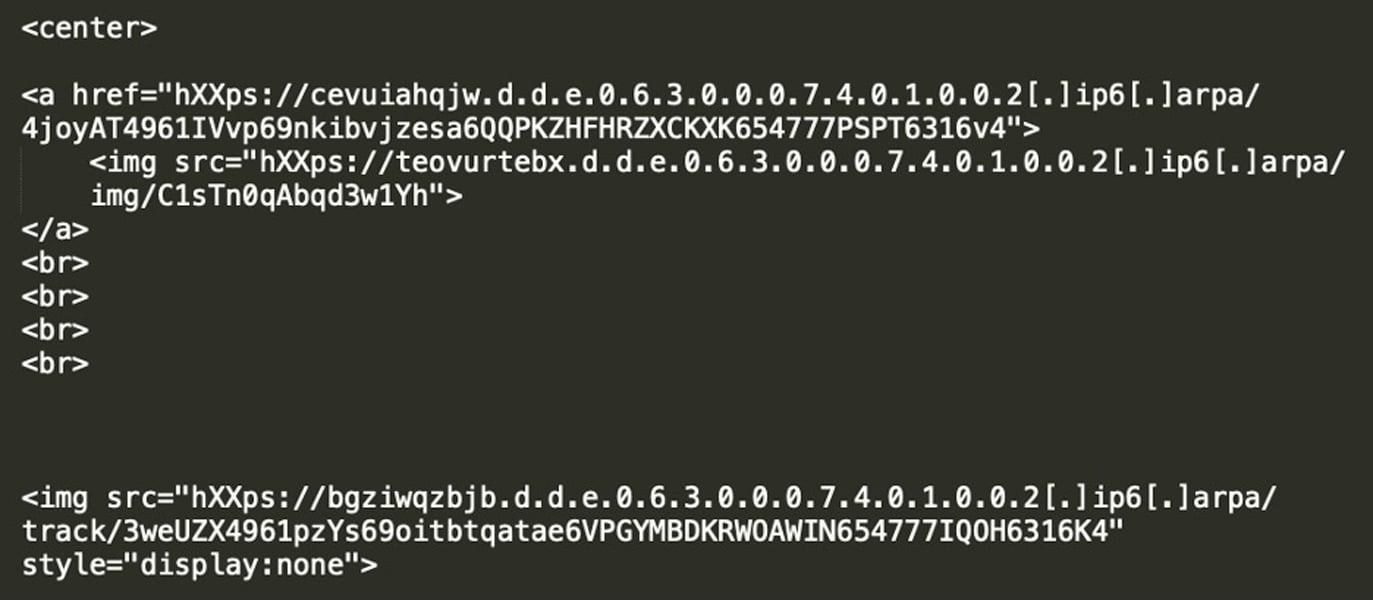
The phishing emails in this campaign use lures that promise a prize, a survey reward, or an account notification. The lures are embedded in the emails as images linked to a reverse IPv6 DNS record, such as “d.d.e.0.6.3.0.0.0.7.4.0.1.0.0.2.ip6.arpa,” rather than a regular hostname, so the target doesn’t see a strange arpa hostname.
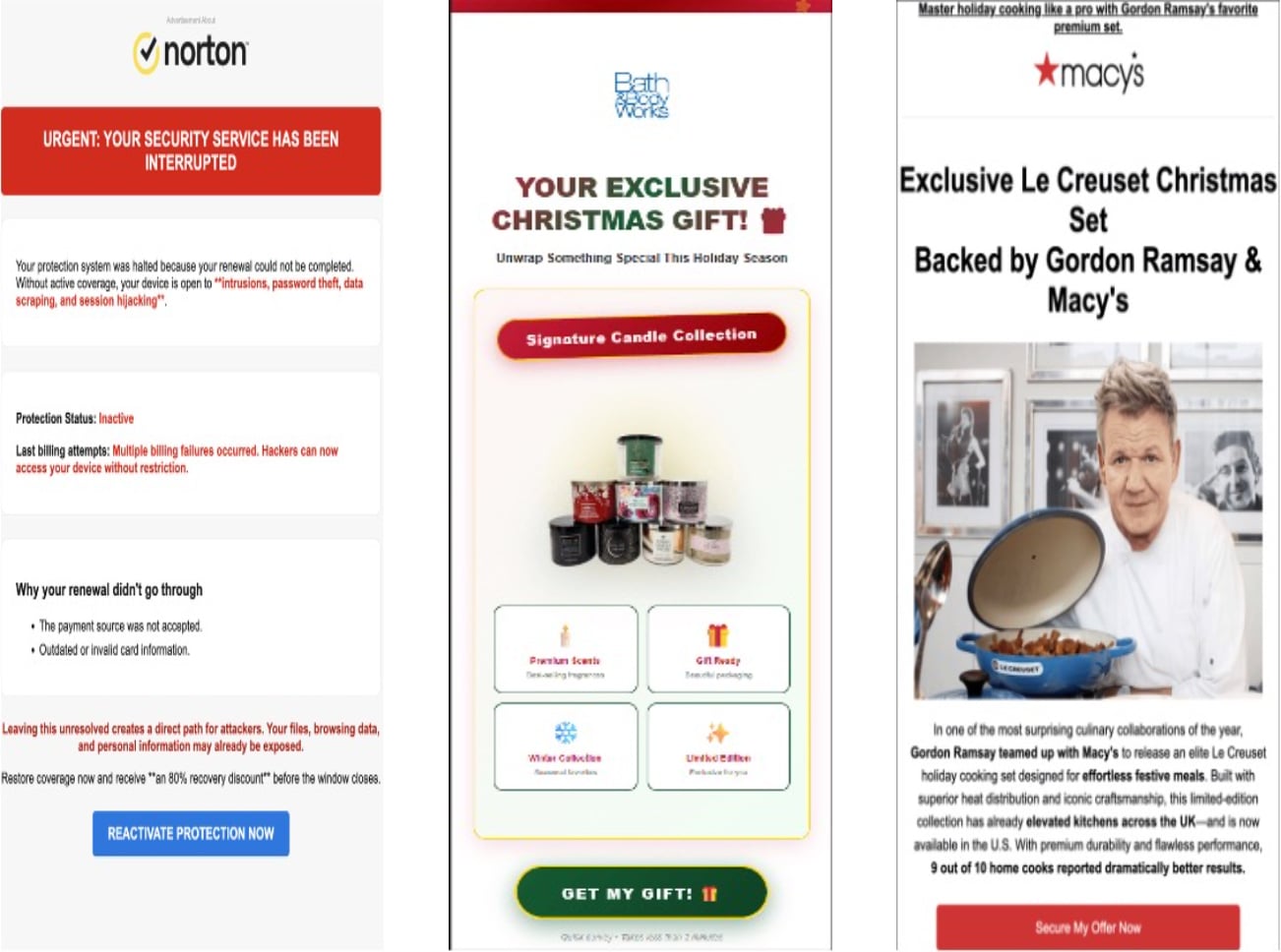
Source: Infoblox
When a victim clicks the phishing email image, the device resolves the attacker-controlled reverse DNS name servers via a DNS provider.
Source: Infoblox
In some cases, the authoritative name servers were hosted by Cloudflare, and the reverse DNS domains resolved to Cloudflare IP addresses, hiding the location of the backend phishing infrastructure.
After clicking the image, victims are redirected through a traffic distribution system (TDS) that determines whether they are a valid target, commonly based on device type, IP address, web referers, and other criteria. If the visitor passes validation, they are redirected to a phishing site. Otherwise, they are sent to a legitimate website.
Infoblox says the phishing links are short-lived, only active for a few days. After the links expire, they redirect users to domain errors or other legitimate sites.
The researchers believe this is done to make it harder for security researchers to analyze and investigate the phishing campaign.
Furthermore, as the ‘.arpa’ domain is reserved for internet infrastructure, it does not include data normally found in registered domains, such as WHOIS info, domain age, or contact information. This makes it harder for email gateways and security tools to detect malicious domains.
The researchers also observed the phishing campaign using other techniques, such as hijacking dangling CNAME records and subdomain shadowing, allowing the attackers to push phishing content through subdomains linked to legitimate organizations.
“We found over 100 instances where the threat actor used hijacked CNAMEs of well-known government agencies, universities, telecommunication companies, media organizations, and retailers,” explained Infoblox.
By weaponizing trusted reverse DNS features used by security tools, attackers can generate phishing URLs that bypass traditional detection methods.
As always, the best way to avoid phishing attacks like these is to avoid clicking on unexpected links in emails and instead visit services directly through their official websites.
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.
Source link


