Akira and Fog ransomware now exploit critical Veeam RCE flaw

Ransomware gangs now exploit a critical security vulnerability that lets attackers gain remote code execution (RCE) on vulnerable Veeam Backup & Replication (VBR) servers.
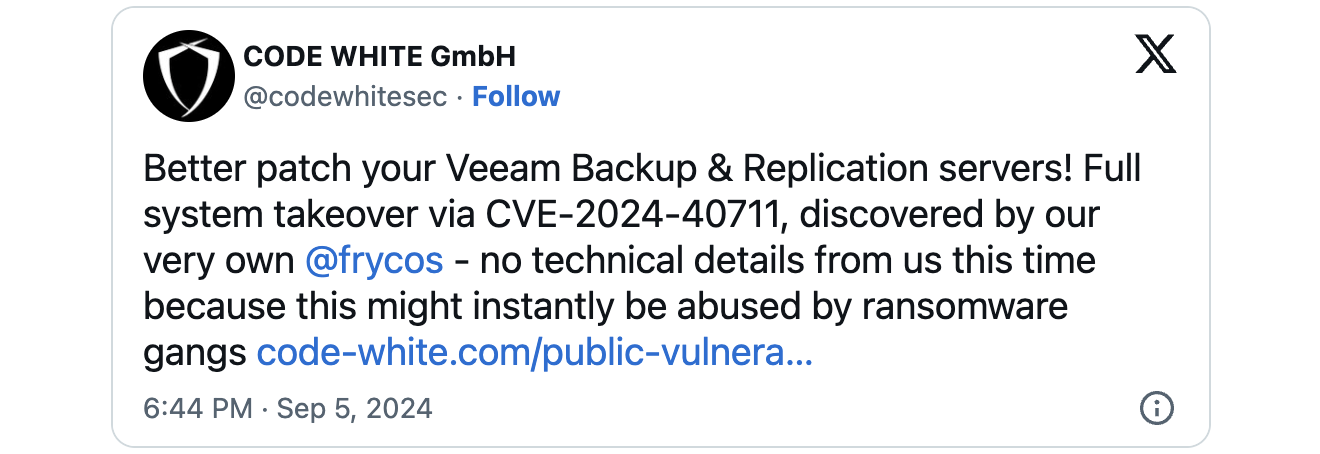
Code White security researcher Florian Hauser found that the security flaw, now tracked as CVE-2024-40711, is caused by a deserialization of untrusted data weakness that unauthenticated threat actors can exploit in low-complexity attacks.
Veeam disclosed the vulnerability and released security updates on September 4, while watchTowr Labs published a technical analysis on September 9. However, watchTowr Labs delayed publishing proof-of-concept exploit code until September 15 to give admins enough time to secure their servers.
The delay was prompted by businesses using Veeam’s VBR software as a data protection and disaster recovery solution for backing up, restoring, and replicating virtual, physical, and cloud machines.
This makes it a very popular target for malicious actors seeking quick access to a company’s backup data.
As Sophos X-Ops incident responders found over the last month, the CVE-2024-40711 RCE flaw was quickly picked up and exploited in Akira and Fog ransomware attacks together with previously compromised credentials to add a “point” local account to the local Administrators and Remote Desktop Users groups.
“In one case, attackers dropped Fog ransomware. Another attack in the same timeframe attempted to deploy Akira ransomware. Indicators in all 4 cases overlap with earlier Akira and Fog ransomware attacks,” Sophos X-Ops said.
“In each of the cases, attackers initially accessed targets using compromised VPN gateways without multifactor authentication enabled. Some of these VPNs were running unsupported software versions.
“In the Fog ransomware incident, the attacker deployed it to an unprotected Hyper-V server, then used the utility rclone to exfiltrate data.”
Not the first Veeam flaw targeted in ransomware attacks
Last year, on March 7, 2023, Veeam also patched a high-severity vulnerability in the Backup & Replication software (CVE-2023-27532) that can be exploited to breach backup infrastructure hosts.
Weeks later, in late March, Finnish cybersecurity and privacy company WithSecure spotted CVE-2023-27532 exploits deployed in attacks linked to the financially motivated FIN7 threat group, known for its links to the Conti, REvil, Maze, Egregor, and BlackBasta ransomware operations.
Months later, the same Veeam VBR exploit was used in Cuba ransomware attacks against U.S. critical infrastructure and Latin American IT companies.
Veeam says its products are used by over 550,000 customers worldwide, including at least 74% of all Global 2,000 companies.
Source link