US targets North Korean IT worker army with new sanctions

The U.S. Treasury’s Office of Foreign Assets Control (OFAC) has sanctioned two individuals and two companies associated with North Korean IT worker schemes that operate at the expense of American organizations.
These schemes involve placing in U.S. firms skilled tech workers with stolen or fabricated identities and using so-called “laptop farms” to hide the true location of the employees.
The workers funnel their earnings to the DPRK regime to fund the regime’s weapons program. They also often steal sensitive data or plant malware to create disruption when their cover is blown.
In the context of cracking down on these operations, U.S. authorities have now sanctioned the following individuals and companies:
- Vitaliy Sergeyevich Andreyev – A Russian national who has worked with DPRK officials since at least December 2024 to facilitate financial transfers supporting the Chinyong Information Technology Cooperation Company. He converted cryptocurrency into nearly $600,000, providing material assistance to the DPRK’s overseas IT worker delegations operating in Russia and Laos.
- Kim Ung Sun – A DPRK economic and trade consular official based in Russia who collaborated with Andreyev to channel funds for the sanctioned IT worker network. He is designated to act on behalf of the Government of North Korea in connection with these revenue-generating activities.
- Shenyang Geumpungri Network Technology Co., Ltd – A Chinese front company tied to Chinyong and composed of a delegation of DPRK IT workers. Since 2021, it has earned over $1 million in profits for both Chinyong and Korea Sinjin Trading Corporation, helping funnel illicit revenues to the DPRK’s weapons programs.
- Korea Sinjin Trading Corporation – A DPRK company subordinate to the Ministry of People’s Armed Forces General Political Bureau, already under U.S. sanctions. It receives directives from DPRK officials regarding the deployment of overseas IT workers and benefits from their earnings.
Blockchain intelligence firm Chainalysis also published details on Andreyev’s Bitcoin wallet, which was used as a deposit address on a mainstream exchange to launder proceeds from DPRK IT workers.
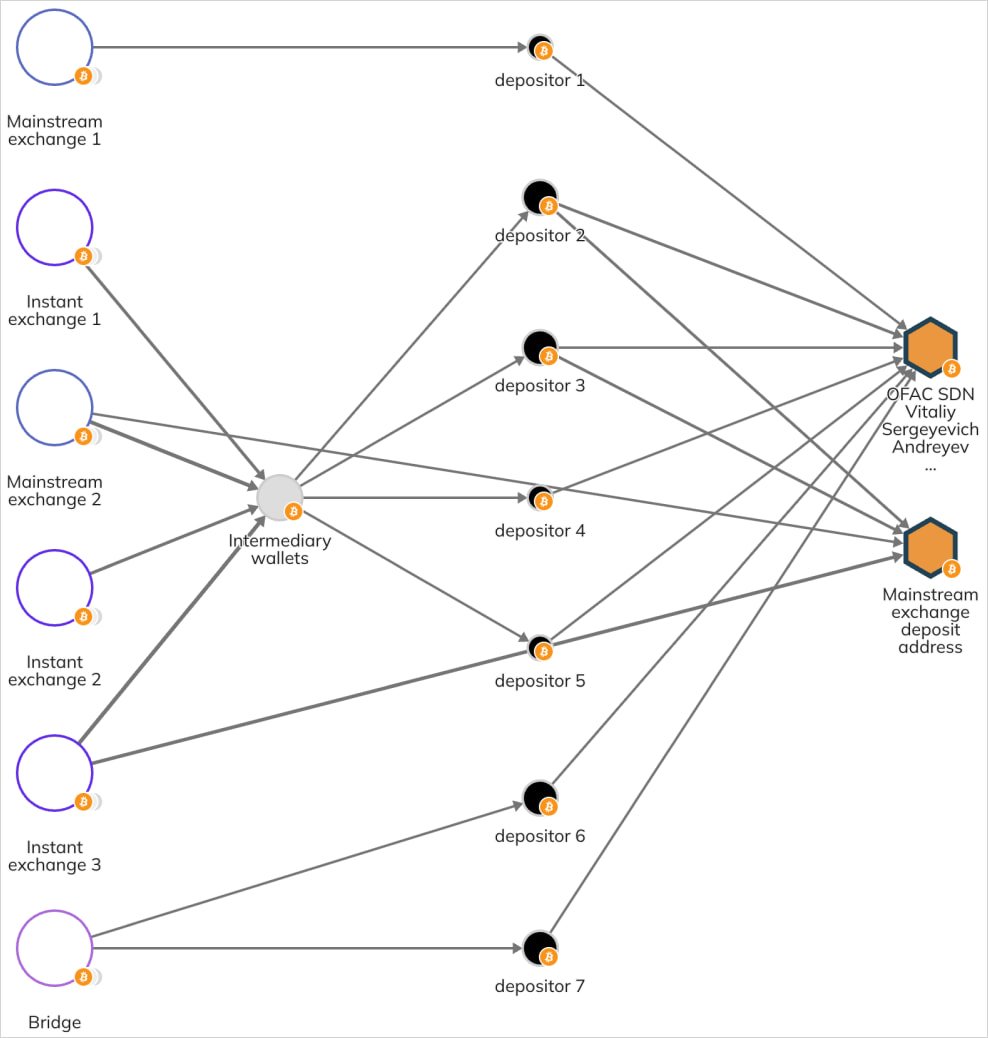
Source: Chainalysis
The effect of these sanctions is a freeze on U.S.-based assets for the designated entities, and all American citizens and businesses are prohibited from engaging in any transactions with them.
This extends as a deterrence outside the U.S., as entities risk being sanctioned or restricted themselves if they choose to conduct transactions on behalf of designated persons and companies.
OFAC is increasingly targeting infrastructure and financial facilitators who help DPRK convert cryptocurrency into usable funds.
Last July, the U.S. authorities sanctioned, charged, or indicted a total of 20 individuals and eight companies in three separate waves of enforcement (1, 2, 3).
Source link


