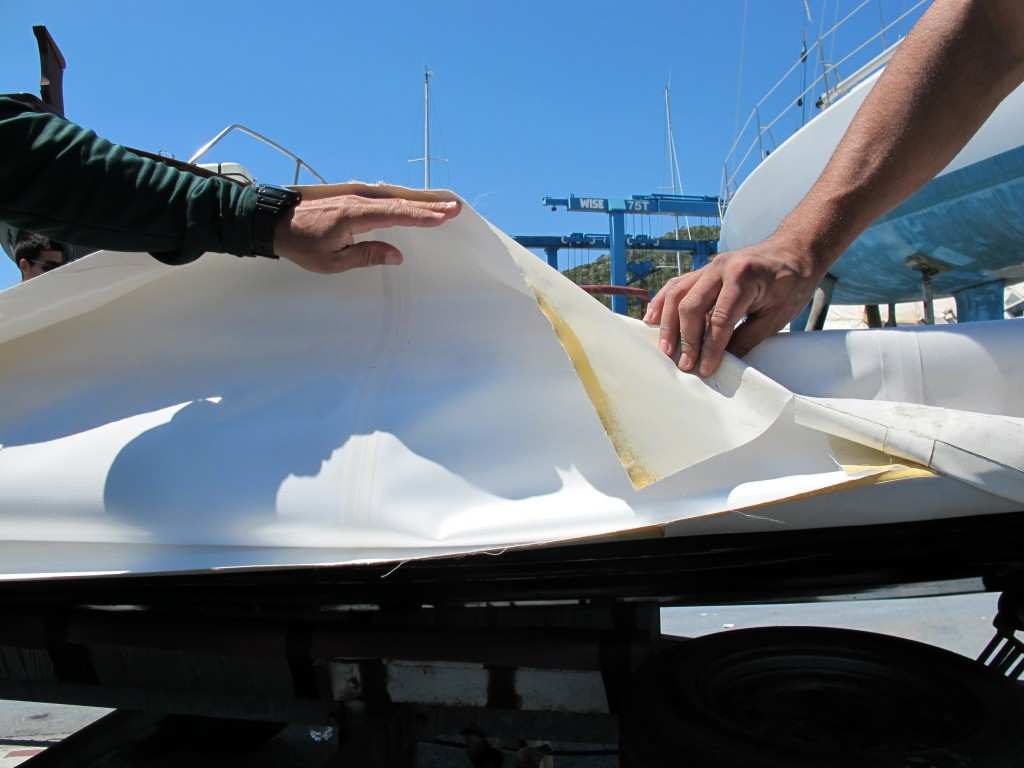
Reparación de Embarcaciones Neumaticas - Suministros Navales Del Sureste. Equipos de seguridad marítima

Reparación de Embarcaciones Neumaticas - Suministros Navales Del Sureste. Equipos de seguridad marítima

Flotadores De Neumaticos Para Piscina Kit de reparación de parches de vinilo para piscinas para piscinas sobre el suelo, balsas inflables, kayak, redondo, reparación de plástico (B, One Size) : Amazon.es: Jardín